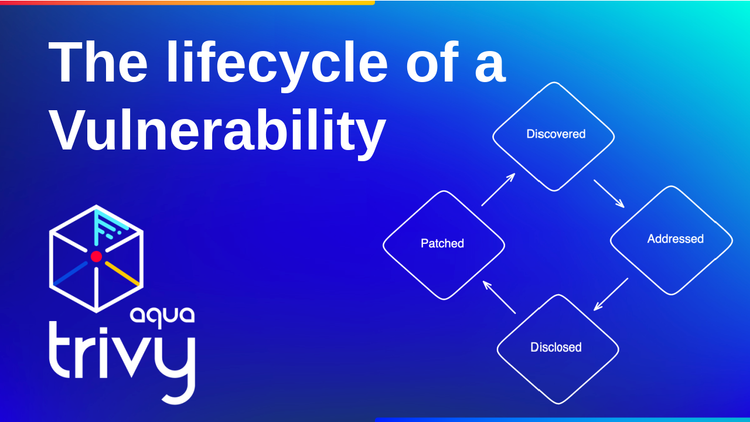
The lifecycle of a Vulnerability
What are vulnerabilities, and where do they come from? In this blog post, we look at the information that security scanners access
Image Signing and Attestation with Trivy, Kyverno, and Cosign
In this tutorial, we are combining three amazing security tools: Trivy, Cosign and Kyverno to sign, attest container images and enforce those through Policies in our Kubernetes cluster.
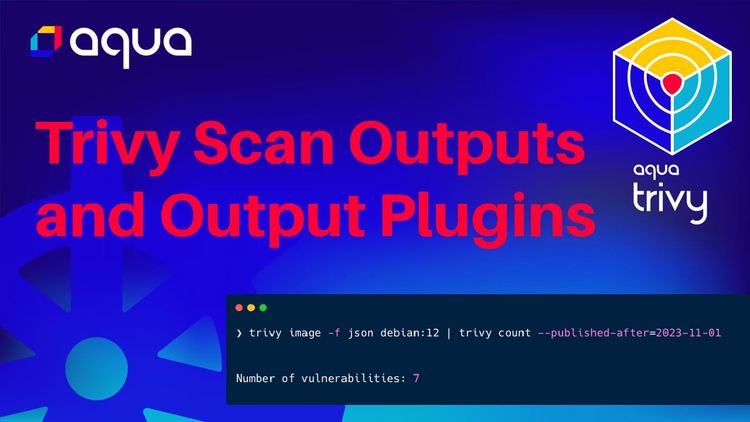
Security Scan Output Options and Output Plugins
Overview of security scan outputs in Trivy, trivy Operator reports and Trivy Output Plugins
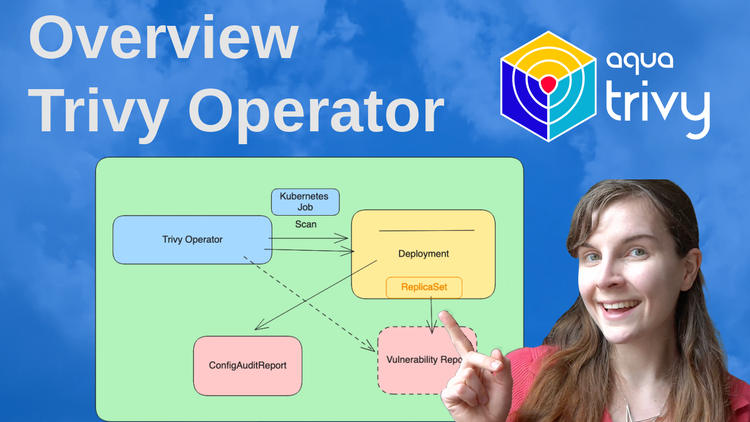
Trivy Operator Overview
Detailed tutorial on creating continuous security scans across your Kubernetes workloads and infrastructure with the Trivy Operator.
Full Tutorial: K8sGPT -- SRE superpowers through AI
In this blog post, I will introduce you to K8sGPT, the project to give Kubernetes Superpowers to everyone.
Getting started with Notary V2
Introduction to Notary V2, a CNCF incubating project -- FULL TUTORIAL
A light introduction to eBPF
In this blog post, we are going to cover eBPF, what it is, why we need it, when to use it and how to get started.
Custom Policy Rules MADE EASY
In this blog post, I show you how you can set up custom checks on your Custom Resource Definitions in Kubernetes.