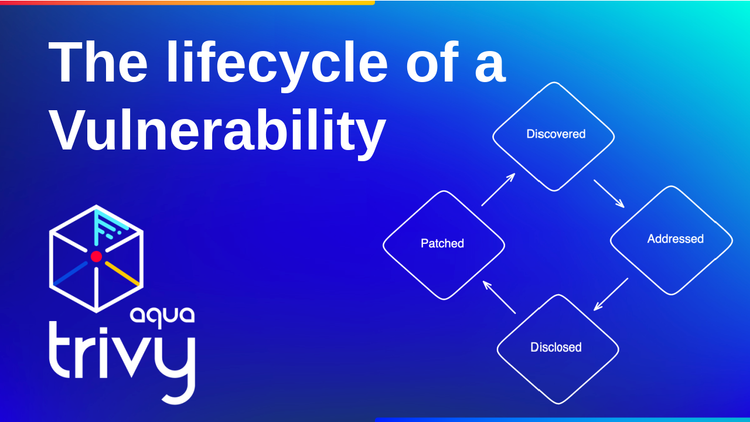
The lifecycle of a Vulnerability
What are vulnerabilities, and where do they come from? In this blog post, we look at the information that security scanners access
Image Signing and Attestation with Trivy, Kyverno, and Cosign
In this tutorial, we are combining three amazing security tools: Trivy, Cosign and Kyverno to sign, attest container images and enforce those through Policies in our Kubernetes cluster.
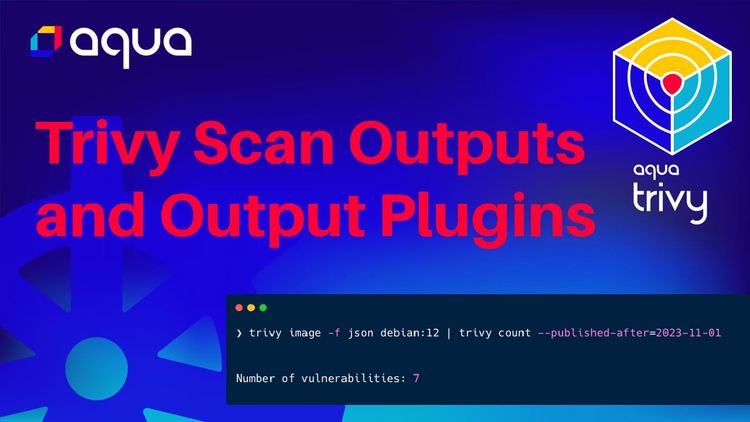
Security Scan Output Options and Output Plugins
Overview of security scan outputs in Trivy, trivy Operator reports and Trivy Output Plugins
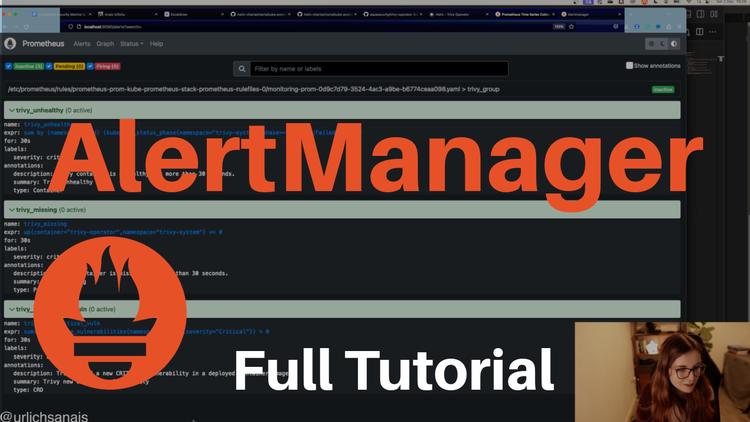
Forwarding Security Metrics to Slack with Prometheus and AlertManager
Full tutorial on using AlertManager and setting up PrometheusRules